The Impact of Covert Impairment on Financial Services Firms
You have spent years gaining customer trust. As an Executive Director or Partner, you completely understand Customer Lifetime Value and its impact on your business bottom line. The legalization of marijuana in many states presents a new challenge in protecting your customer data and keeping their trust.
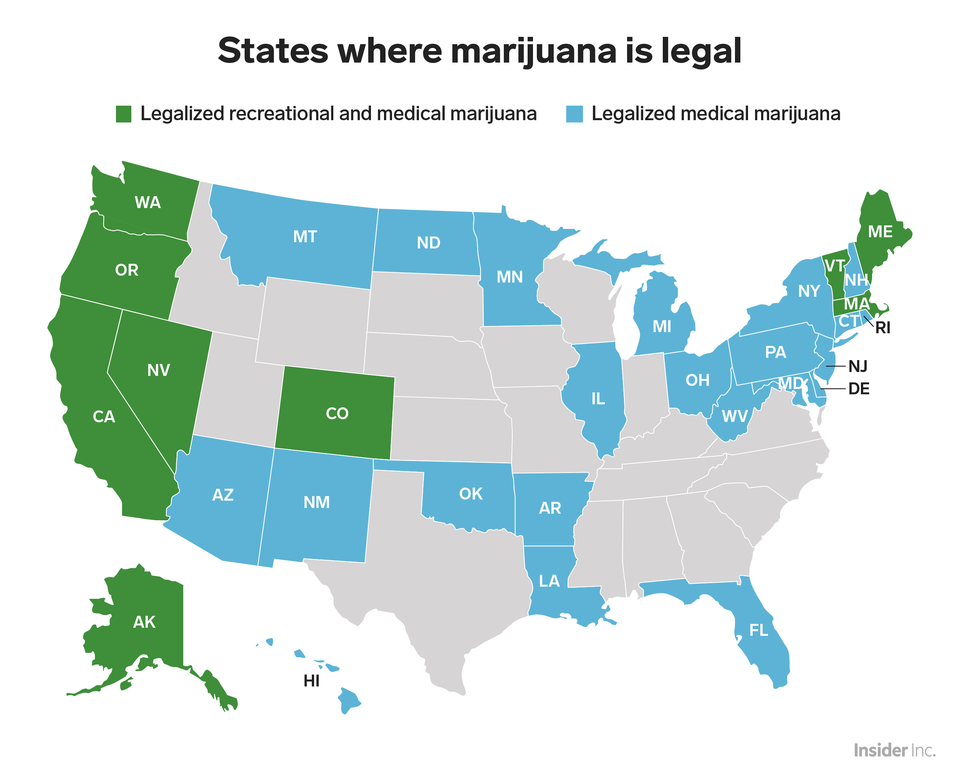
Table of Contents
Introducing a new term: Covert Impairment
“Cannabis impairment can impact decision-making skills and sensory perceptions. Consider the possibility of an employee working from home, which for most, can be a relaxing and private workspace. Suppose that while Jack is writing code and programs for an IT firewall and security system he’s updating for his firm, he decides to smoke a joint over lunch to chill out a bit. After a relaxing lunch, he feels fine around 1:30 p.m. to go back to work. It’s just 60 minutes after inhaling his one joint, but his impairment window at its THC dosing level is four to five hours.”
Read more about Managing the risk of ‘covert impairment’ after the legalization of cannabis.
In today’s digital world, customer data is one of the most valuable currencies. Unfortunately, that makes it an incredibly attractive target for hackers, phishers, and other cyber criminals. In fact, an estimated 158,727 pieces of customer data are stolen every single hour.
It’s not just cyber criminals that leave you vulnerable to data breaches, though. Simple human error can lead to the unintentional release of customer data, and the consequences for your business can be equally devastating.
Legal Implications
At present, federal legislation governing data protection tends to be sector-specific, while state legislation focuses on protecting the data of individual consumers.
It can be hard to keep track of which regulations you need to adhere to, but the basic principle is that you need to take reasonable measures to protect personally identifiable or sensitive information about your customers — think names, addresses, social security numbers, or credit card information, for example.
Depending on your state and sector, you might be required to do any number of the following:
- Encrypt personally identifiable information

- Destroy sensitive information in a way that makes it unrecoverable
- Specify exactly how you plan to use the information you collect
- Restrict the sale of information for marketing purposes
- Publish detailed data security plans
- Notify affected customers of data breaches within a set time frame
If you fail to meet your obligations and a data breach occurs, you may face heavy fines and be held liable for damages suffered by your customers. In some sectors and/or jurisdictions, you may even lose your license to conduct business altogether.
Public Relations Damage
Research has found that in the event of a cyber attack, as many as 60% of your customers consider leaving, and around a third actually do, even if they weren’t personally affected.
It makes sense — your customers are trusting you with their most personal of data, and a breach can seriously shake their confidence in your ability to keep that data (and them) safe. Very few businesses can survive the loss of one third of their customers, and chances are yours is one of them.

Financial Loss
With legal consequences, public relations damage, and customer decline comes financial loss. Whether you’re paying steep fines or losing out on sales, your business takes a huge monetary hit from a data breach. The cost of a breach for an average small business is approaching $150 million, which again, most businesses simply can’t afford.
Time to Call in the Experts?
Even the best-protected and most vigilant companies can fall victim to a data breach, so it’s important to take a proactive approach to keeping your customer data safe and secure. Ultimately, the best way to do this is to get a helping hand from the professionals.
At Fairdinkum, we help businesses like yours to secure their customer data, protect their reputation, and avoid costly legal and financial consequences. You can download Fairdinkum’s free Security Audit Checklist to help you to find your weak spots before cyber attackers do, or contact us now for a free, no-obligation consultation.
For more details on cyber security, visit our Cyber Security page.